What is automated provisioning? Plus real-world examples
.avif)
Auto-provisioning has seemingly gotten more popular over the last few years.
The reasons aren’t hard to discern; it allows B2B SaaS companies to increase product usage and security for their customers, and it gives IT/security teams a way to reduce onboarding time and remove unused application seats automatically.
To help your organization use auto-provisioning effectively, we’ll walk through what it is, its benefits, examples of using it, and some best practices for implementing it in your product. We'll also introduce you to some auto-provisioning platforms for both internal and product/customer-facing use-cases.
What is automated provisioning?
It’s the automated assignment of employee permissions, such as software seats or billing controls, based on the employee’s department, team, among other factors. Auto-provisioning also includes auto-deprovisioning, which means revoking access if those parameters change in a certain, predefined way.
Benefits of automated provisioning
Here are some of the top benefits to keep in mind:
Provides time savings
According to a study by Vendr in 2023, the average SaaS company uses 130+ SaaS solutions. Attempting to keep every application up to date with new hires and leavers can therefore be an impossible job. Adding fuel to the fire, creating a new user oftentimes requires filling out a variety of fields, like first name, last name, email address, role, and org chart information, which makes this type of data entry work all the more overwhelming to perform over time.
Automated provisioning based on whether someone has joined a company or departed can significantly reduce the amount of time it takes to manually fill out information for each user.
This can also benefit SaaS vendors; decreasing the amount of time it takes to onboard new users to their product can be a quick way to improve product adoption and stickiness.
Improves security
Although deprovisioning is often a critical step in employee offboarding processes, it’s easy to miss departed users in a few applications when security and IT has so many applications to remove them from. This can result in every security team’s nightmare: seeing departed employees still have access to critical company information.
Automated removal of recent departures can provide a sense of relief for security teams who may be worried about scaling security and application access as a company grows.
Increases product usage
One reason why a lot of companies may end up suffering from churn is that their clients fail to fully adopt and use their product. Even if one person is extremely passionate about a product, it’s hard justify the investment; you need several individuals, if not entire teams, to become active users.
Automatically issuing access to every employee is an easy way to remove the barriers for entry for new users. This can be especially true for new hires. Reason being, when employees first joining a company, they’ll get used to the first few vendors they're introduced to and incorporate them into their workflows.
Reduces human errors
Keying in data manually is an extremely error-prone activity. In some cases, it can lead to seemingly innocuous errors, like misspelling someone’s name. But in other cases, these errors have consequential downstream effects.
For instance, if an employee’s email address is misspelled, they may not receive an invite for an event; or, if an employee’s role is incorrect, they may get additional permissions in an application and access information that isn’t meant for them.
There are so many ways in which human error can cause major issues, and preventing this through auto-provisioning can be a huge relief for security teams.
Related: Benefits of automating user provisioning and deprovisioning
How automated provisioning works
Here’s how you can implement auto-provisioning workflows:
Grant new hires access to an application on their first day
Here is a recommended flow that we've seen for auto-provisioning applications on behalf of new hires:
1. Build integrations with HRIS / SCIM providers.
2. Build a user interface that supports your customer auto-provisioning new users based on information in the HRIS / SCIM provider.
3. Once an HRIS / SCIM has added a new employee, create a new user for that employee in your application.
4. Send the new hire an email informing them of their new account in the application.
5. Allow them to onboard with their information and org chart information filled out based on information from the HRIS.
6. Send an email to IT / security informing them of the new user account.
Change a user’s permissions when they switch teams
When an employee moves to a new team and works under a new manager, the amount of access they are privy to may change. Through managing user permissions based on org chart information, IT / security teams can offload some of the responsibilities of changing permissions to an application.
Here is a recommended flow we've seen:
1. Build integrations with HRIS / SCIM providers.
2. Build a user interface that supports your customer auto-provisioning permissions based on org chart information in the HRIS / SCIM provider.
3. Once an HRIS / SCIM has notified you of a change in the org chart, modify the corresponding user’s permissions in your application according to the permissions that your customer has set for this user’s new role.
4. Send an email to IT / security informing them of the permission change.
Real-world examples of automated provisioning
To help bring automated provisioning to life, let’s break down how a few companies incorporate it in their products.
Issuing and deactivating corporate cards
Ramp, a leading financial operations platform, offers HRIS integrations to help customers add and remove users easily.
For provisioning users:
1. Once a user is added in the integrated HRIS, Ramp determines whether the user already exists in the platform through the user’s email address or phone number.
2. Assuming the user doesn’t already exist, Ramp adds them in the “To Invite” list within the Team Updates tab. From there, an admin can review the user and decide whether to add them to Ramp.
3. If the user is added to Ramp, Ramp auto-assigns the appropriate cards with the correct spend limits based on the rules the admin has set—along with the user’s job title, department, and address.
For deprovisioning users:
1. Once a user is removed in the integrated HRIS, Ramp determines whether the user exists in the platform by using the user’s email address or phone number.
2. If the user exists, Ramp adds them to the “To terminate” list within the Team Updates tab. An admin can then review the user and decide whether to remove them in Ramp. Also, the admin(s) will receive daily emails about the user from Ramp to ensure they get removed quickly.
3. An admin can go on to remove a user in the Team Updates tab within a few clicks.
Anish Ravipati, a staff software engineer at Ramp, breaks down how, exactly, these integration flows work here:
Automating equipment shipments and returns
Electric, an IT asset management platform, uses auto-provisioning to procure and ship equipment to incoming new hires and to initiate equipment returns for departing employees.
Here’s more on each process:
1. Once a user is marked as hired in the integrated HRIS, an admin in Electric gets notified and goes on to select the group that the incoming employee should belong to (e.g., R&D).

2. Based on this group, and the other data that’s added to the new hire’s profile (e.g., address), Electric goes on to purchase the right set of equipment and ship it well in advance of the new hire’s start date.
Electric also identifies the applications they need access to, and it can go on to provision the new hire with access to these apps—along with the right set of permissions for each—by the start of that employee's first day.
For automated deprovisioning:
- Once an employee is marked as terminated in the integrated HRIS, Electric kicks off the offboarding workflow that the user has defined. This can include sending a QR code for the employee to print out and include on the boxes of equipment they need to return. And it can take the form of removing the employee’s access to applications by the end of their last day
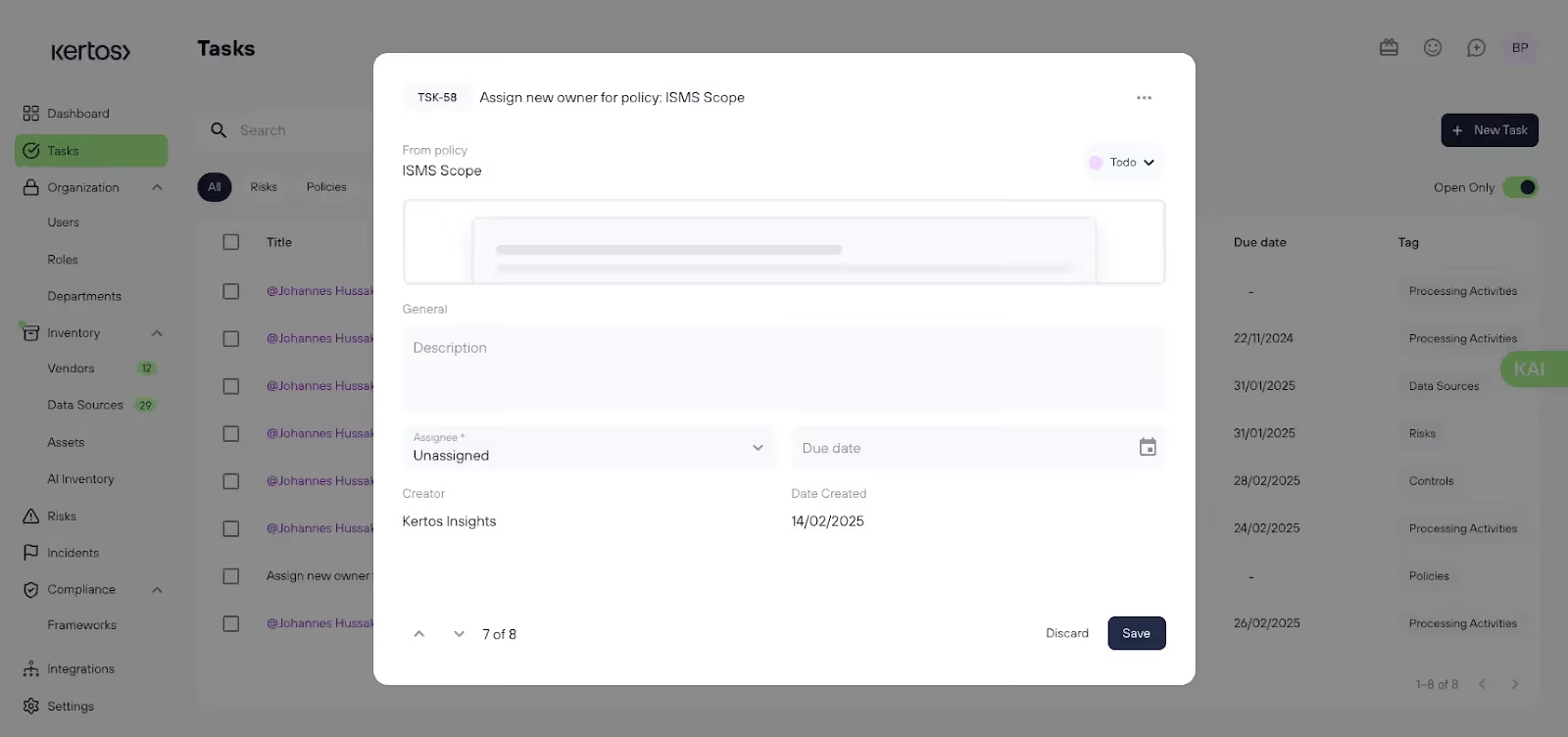
Streamlining compliance and security processes
Kertos, a compliance automation platform, uses automated provisioning to power several critical security workflows.
Here are just a few:
- Once a user is added to the integrated HRIS, Kertos can add the new hire to its system and—based on their role, department, location, and rules the company sets in the app—assign the new hire certain tasks
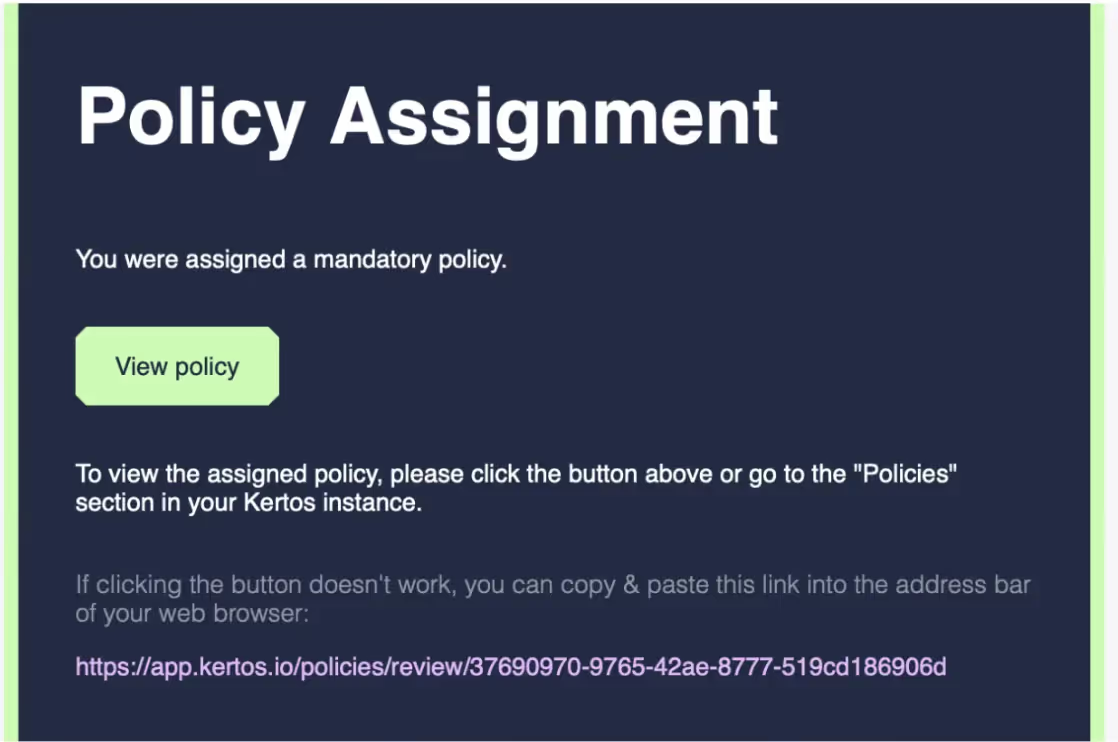
- Once an employee is marked as terminated in the integrated HRIS and they were the owner of a particular policy, a task gets created in Kertos to assign a new policy owner
Giving rewards and recognition based on key employee milestone events
Bonusly, a peer-to-peer recognition platform, uses auto-provisioning workflows to streamline recognition awards for new hires and employees who are leaving.
Here’s more on each flow:
1. Once an employee is added in the integrated HRIS, they’re also added in Bonusly.
2. Assuming the admin has set up a reward for new hires, the employee can receive a certain amount of points on their first day, which can potentially vary based on their role and department.

If an employee’s end date is selected in the integrated HRIS and an admin has set up an award for departing employees that thanks them for their contributions, Bonusly can send that employee a thank you award shortly before they leave.
Best practices for auto-provisioning
Auto-provisioning and deprovisioning is one of Merge’s most popular use cases, and we’ve learned a lot about best practices through seeing our customers implement it in their products.
Here are some recommendations for adding auto-provisioning to your products:
Integrate with a variety of HRIS / SCIM providers
The HRIS / SCIM landscape is extremely fragmented. If you only integrate with 1-2 HRIS / SCIM providers, it’s unlikely that you’ll cover most of your customers.

Build an intuitive UI that allows your customers to customize their auto-provisioning
Each company will likely have varied processes and security requirements for their team members. Generally, the larger the company, the more stringent the security requirements are. IT / security team members at these companies will likely want to customize the access levels that are granted on a more granular level.
Building a UI that your customers can modify according to their own processes ensures that they're able to continue auto-provisioning/deprovisioning users in your product over time.
Build a proactive alerting system that informs IT / security teams of user permission changes as they occur
Automating user changes based on an HRIS / SCIM integration can be slightly nerve-wracking, as there's a small chance that an accidental setting causes issues. To ensure that your IT / security team becomes aware of any errors and addresses them quickly, you can send them notifications whenever there are permission changes.
Ramp integrates with 40+ HRIS systems through Merge to auto-provision users
Automated provisioning tools
For product use cases, there are several integration options for building auto-provisioning:
- Native integrations
- Embedded iPaaS
- Unified APIs (ex. Merge)
For internal-use cases, there's a growing ecosystem of applications focused on helping you manage your users in your company’s applications:
Related: A guide to API integration middleware
Introducing Merge
Merge is the leading unified API solution that lets your developers build to a single unified API to add 40+ HRIS, Payroll and SCIM integrations to your products. Once connected, Merge maintains the integrations with 3rd-party API providers on your behalf.
In addition, we work with hundreds of companies to add auto-provisioning and deprovisioning to their products; it's one of our most popular use cases.
You can learn more about Merge and how you can use it to build auto-provisioning workflows by scheduling a demo with one of our integration experts.







.png)
.png)

