Table of contents
Just for you
API integration security: what it is and best practices

Your internal and customer-facing API integrations often access and sync sensitive data.
This includes anything from employees’ social security numbers to your business’ financial data to your clients’ credit card information.
Failing to provide adequate security controls for this data can compromise your ability to pass audits like SOC 2 Type II and meet critical data protection and privacy regulations, like GDPR. Just as important, it can lead you to lose clients’ trust and damage your reputation in the market.
To help you avoid these negative consequences—while reaping the benefits of API integration—we’ll break down 5 API integration security best practices. But first, let’s align on the definition of API integration security.
What is API integration security?
It’s a set of practices and tools you use to protect the data and applications you’ve connected. The end goal is to keep your employees’, clients’, prospects’, and partners’ data safe from unauthorized access.
It's worth noting that you can apply API integration security to your customer-facing integrations and your internal integrations.
Related: What are API access controls?
API integration security best practices
While there are countless measures you can take, we’ll break down several that you should prioritize.
1. Confirm that the API provider meets your security requirements
3rd-party APIs differ from one another in countless ways—and security is no exception.
To ensure that a specific 3rd-party API takes the necessary precautions to keep data secure, you can review their API documentation. When doing so, you should look at the following (among other items):
- Authentication and authorization mechanisms: confirm that the API provider offers common protocols, like OAuth or OpenID Connect
- Encryption policies: determine if they use HTTPS when data is in transit, and even offer more advanced encryption methods (e.g., Perfect Forward Secrecy)
- Data privacy and compliance: see if the API provider complies with all of the data privacy and compliance requirements you care about
2. Adopt robust error handling processes
Your integrations can behave in unintended ways that leave your organization vulnerable (e.g., sensitive data can get leaked). In addition, depending on the industry you’re in, you may face compliance checks that test your ability to identify and address certain issues.
You can tackle both of these areas effectively by implementing an error handling process that lets your team identify, diagnose, and resolve issues quickly and successfully.
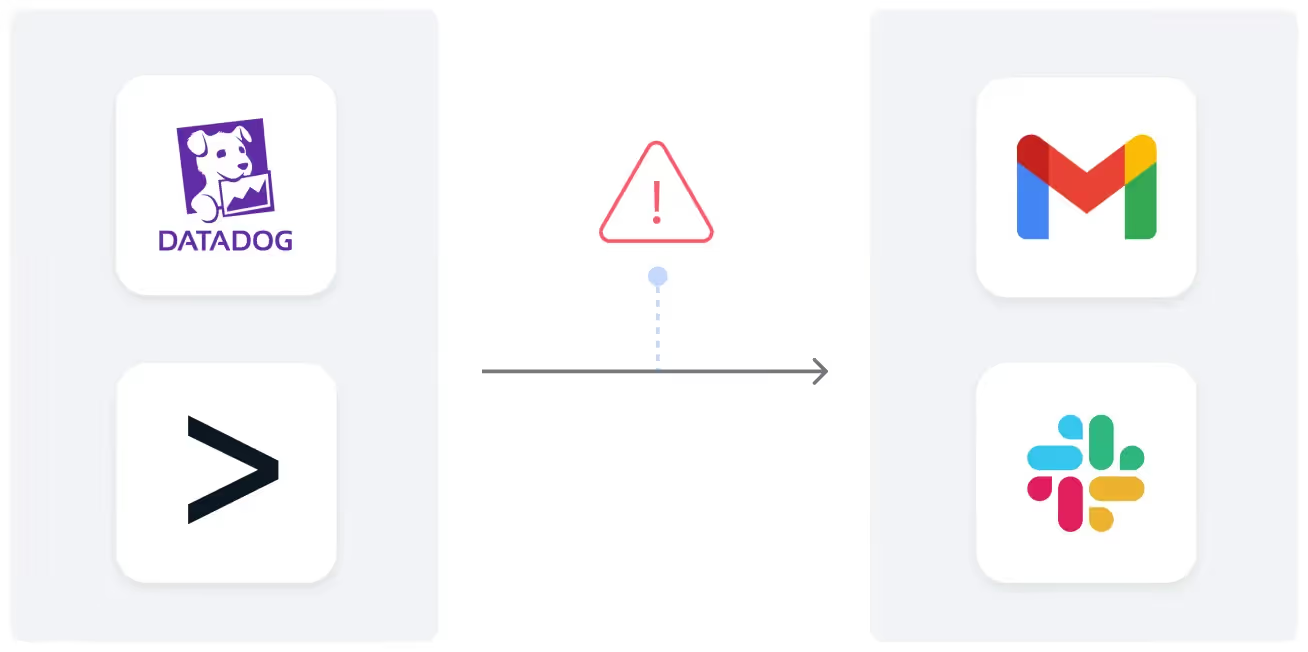
For instance, you can integrate your monitoring tool (e.g., Datadog) with your business communications platform (e.g., Slack) and build a workflow where once a certain type of issue occurs (according to the associated log), a specific channel in your business communications platform receives a message that includes details from the log.
3. Take several measures to protect your API keys/tokens
Whether you’re using API keys or tokens to authenticate to an API, it’s critical that you take the necessary precautions to keep them protected.
Exposing them can lead an attacker to make API calls on your behalf, which potentially allows them to access sensitive data and perform actions that compromise your employees and/or clients.
Fortunately, there’s a number of ways you can protect your API keys and tokens.
You can avoid hardcoding them in your source code—in case a malicious actor accesses this code; implement features that limit the lifespan of your tokens/API keys, such as time-based or event-based expiration; and use a secure vault service like AWS Secrets Manager to store your credentials in a secure location.
Related: Best practices for using API sandboxes
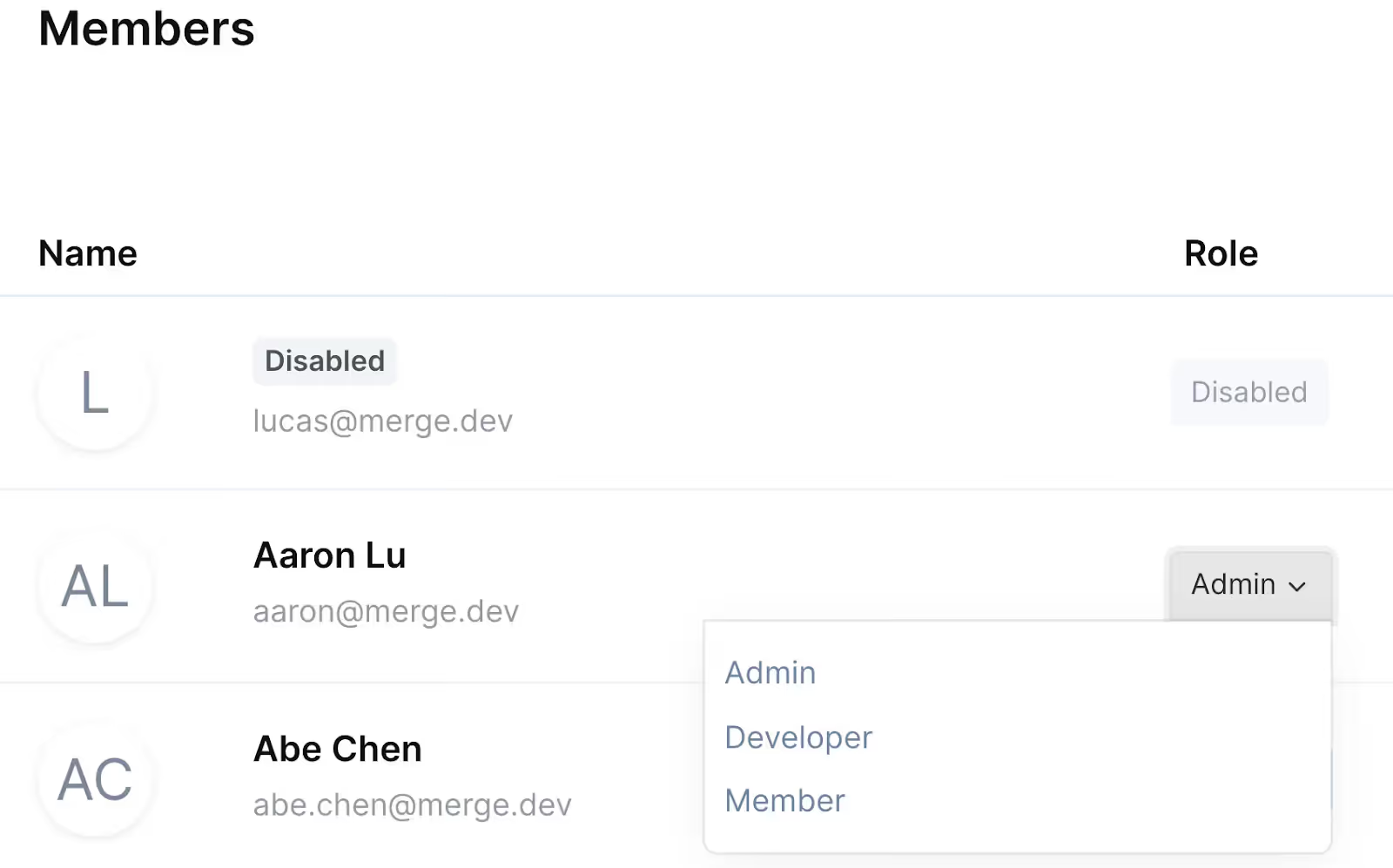
4. Leverage role-based access control if it’s available
If you’re using an API integration tool, you’ll want to be careful when you’re provisioning users, as you don’t want anyone to access data that can compromise your employees, clients, and, more generally, your ability to comply with data privacy and protection regulations.
To that end, you should invest in an integration tool that provides role-based access control, and, when using it, you should follow the principle of least privilege. In other words, users should only get access to the data they absolutely need to carry out their work.
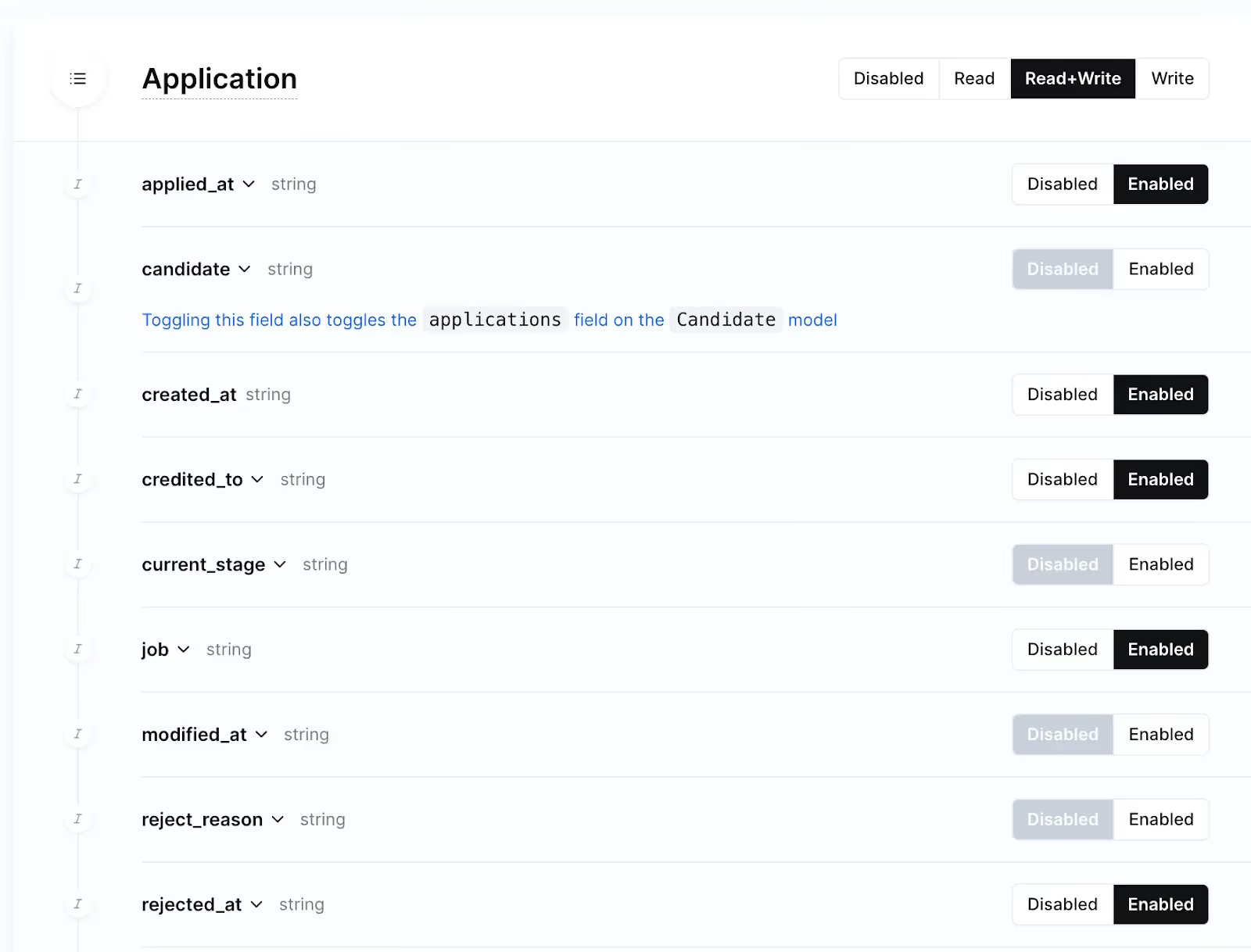
5. Minimize the objects and fields you’re able to access and sync
Using a 3rd-party integration solution, you may be able to pick and choose the objects and fields you’re able to access and interact with. If you can, you should—similar to the previous tip—follow the principle of least privilege.
Just by following this best practice, you’re effectively preventing any potential issues that can come with collecting and accessing sensitive data.
Related: A guide to building secure integrations
Benefits of having secure API integrations
By implementing the best practices above, your organization is set to benefit in a variety of ways, especially for customer-facing integrations.
Enables you to comply with key data protection measures and regulations
Complying with security frameworks like GDPR, SOC 2 Type II, ISO 27001, HIPAA, and others can help you close prospects, prevent costly fines, avoid litigation, and sustain trust with customers—which can help you keep their business over time.
Preserves your reputation in the market
If, for whatever reason, sensitive data leaks from a customer-facing API integration, your relationship will not only deteriorate with the affected customer but also with other customers and prospects—whether that’s through word of mouth, an online review, or even media coverage.
Secure API integrations prevent you from experiencing the above; and they can even give you a competitive advantage when rivals experience security issues.
Helps you upsell customers and capture more revenue
Many of the security features you build around your customer-facing integrations can be reserved for your most expensive price plan and/or purchased as add-ons.
Assuming these features are critical for enterprise companies, this will likely lead to additional sales opportunities for your business.
Keep your customer-facing integrations secure with Merge
Merge—which offers a single API that lets you add hundreds of integrations to your product—provides several features and capabilities to keep your clients’ data safe.
In addition to the features we’ve highlighted above, Merge offers Audit Trails, which allows your account admin(s) to oversee and analyze all of the activities taking place in your account; and Merge offers multi-factor authentication for all users in your organization.
Merge also adhere to a variety of industry-standard compliance frameworks, which include GDPR, HIPAA, ISO 27001, CCPA, and SOC 2 Type II.
You can learn about Merge’s security controls, certifications, and more by connecting with one of our integration experts.
API integration security FAQ
In case you have any more questions on API integration security, we’ve addressed several more below.
What tools can you use to test API integrations' levels of security?
You can use Postman to test an integration’s authentication and authorization implementation; see how the integration handles injection attacks; determine how it handles denial-of-service or distributed denial-of-service attacks, and more.
You can also use tools like Apache JMeter and SoapUI to run tests that help you determine whether an integration is secure at scale.
Are 3rd-party integration solutions that prioritize security typically more expensive?
They may be more expensive (e.g., a few thousand dollars more per year). But given the costs associated with security incidents, from reputational damage to potential fines, it’s well worth prioritizing integration solutions that have built out enterprise-grade security features and abide by the most stringent security frameworks.
What is the difference between API security and API integration security?
API security refers to the specific processes and tools used to safeguard an endpoint(s); while API integration security has the same definition but applies it to the specific applications and data that's connected.





.png)
%20(6).png)
.png)

